The settings below must be filled out correctly and saved before you will see the Metadata tab to continue.
##### Service Provider Fields (Configured in OPSCOM) These fields define how OPSCOM will interact with your Identity Provider.`` ` ``<``samlp:Response` `xmlns:samlp``=``"urn:oasis:names:tc:SAML:2.0:protocol"` `xmlns:saml``=``"urn:oasis:names:tc:SAML:2.0:assertion"` `ID``=``"_aa1963115aa6490e728c7376f4c8849813bbb..."``>` ` ``...` ` ``<``saml:Assertion` `xmlns:xsi``=``"http://www.w3.org/2001/XMLSchema-instance"` `xmlns:xs``=``"http://www.w3.org/2001/XMLSchema"` `ID``=``"_9efd79bf6425983ee9176f3d33a99d1a9176180..."``>` ` ``...` ` ``<``saml:Subject``>` ` ``<``saml:NameID` `SPNameQualifier``=``"MinionOpsComStaff"` `Format``=``"urn:oasis:names:tc:SAML:2.0:nameid-format:transient"``>_7a426e0be71f14c1f349db00d7d543b6f7dcb52baa` ` ``<``saml:SubjectConfirmation` `Method``=``"urn:oasis:names:tc:SAML:2.0:cm:bearer"``>` ` ``<``saml:SubjectConfirmationData` `NotOnOrAfter``=``"2021-08-24T16:00:41Z"` `Recipient``=``"https://minion-3.dev.parkadmin.com/auth/saml2/MinionOpsComStaff/acs"` `InResponseTo``=``"ONELOGIN_bb8a09203c888cf59af4c621a71cfa8f7559c016"``/>` ` ``` ` ``` ` ``<``saml:Conditions` `NotBefore``=``"2021-08-24T15:55:11Z"` `NotOnOrAfter``=``"2021-08-24T16:00:41Z"``>` ` ``<``saml:AudienceRestriction``>` ` ``<``saml:Audience``>MinionOpsComStaff` ` ``` ` ``` ` ``<``saml:AuthnStatement` `AuthnInstant``=``"2021-08-24T15:34:46Z"` `SessionNotOnOrAfter``=``"2021-08-24T23:34:46Z"` `SessionIndex``=``"_a7a68666092117d24aab8adecf1b0830622855b85..."``>` ` ``<``saml:AuthnContext``>` ` ``<``saml:AuthnContextClassRef``>urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport` ` ``` ` ``` ` ``<``saml:AttributeStatement``>` ` ``<``saml:Attribute` `Name``=``"uid"` `NameFormat``=``"urn:oasis:names:tc:SAML:2.0:attrname-format:basic"``>` ` ``<``saml:AttributeValue` `xsi:type``=``"xs:string"``>6ddf4027-3397-4e45-8628-0189f60fe91e` ` ``` ` ``<``saml:Attribute` `Name``=``"full name"` `NameFormat``=``"urn:oasis:names:tc:SAML:2.0:attrname-format:basic"``>` ` ``<``saml:AttributeValue` `xsi:type``=``"xs:string"``>Sarah Knowles` ` ``` ` ``<``saml:Attribute` `Name``=``"email"` `NameFormat``=``"urn:oasis:names:tc:SAML:2.0:attrname-format:basic"``>` ` ``<``saml:AttributeValue` `xsi:type``=``"xs:string"``>sknowles@tomahawk.ca` ` ``` ` ``` ` ``` ` ``` |
The exact sample values from our test system may differ from your actual SAML system attributes.
##### Translations Tab The **Translations** tab allows you to customize the text displayed on your login button from the user side. You can create as many different translations as are available in your system (e.g., English and French). This ensures that the SSO login experience is localized for your users. [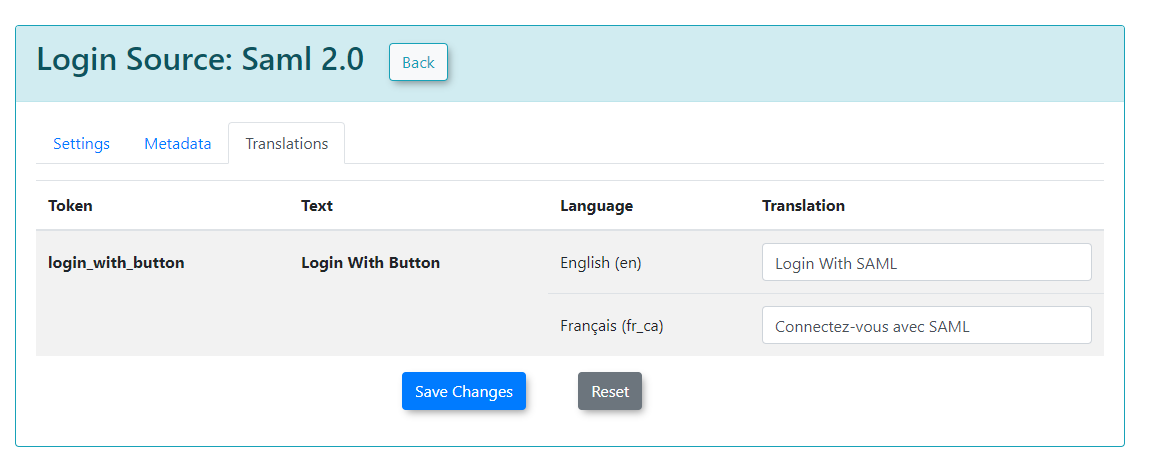](https://opscom.wiki/uploads/images/gallery/2024-06/0Bpimage.png) --- ### Best Practices & Considerations